
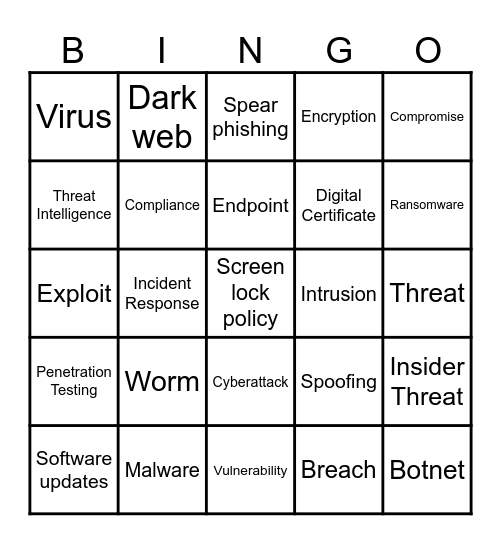
This bingo card has 45 words: Reusing passwords, Screen lock policy, Phishing, Software updates, Awareness, Breach, Spear phishing, Zero-day, Compromise, Malware, Encryption, Intrusion, Cyberattack, Worm, Backups, Vulnerability, Training, Exploit, Personally identifiable information (PII), Ransomware, Dark web, Scareware, Multi-factor authentication (MFA), Virus, Whale phishing, Threat, Trojan, Patch, Spoofing, Penetration Testing, Social Engineering, Insider Threat, Backdoor, Security Policy, Data Loss Prevention (DLP), Incident Response, Cyber Hygiene, APT (Advanced Persistent Threat), Botnet, Endpoint, Threat Intelligence, Digital Certificate, Honeypot, Compliance and Threat Actor.
RGL Cybersecurity Bingo | RGL Cybersecurity Bingo | RGL Cybersecurity Bingo | RGL Cybersecurity Bingo (for all Teammates) | RGL Cybersecurity Bingo
Share this URL with your players:
For more control of your online game, create a clone of this card first.
Learn how to conduct a bingo game.
With players vying for a you'll have to call about __ items before someone wins. There's a __% chance that a lucky player would win after calling __ items.
Tip: If you want your game to last longer (on average), add more unique words/images to it.