
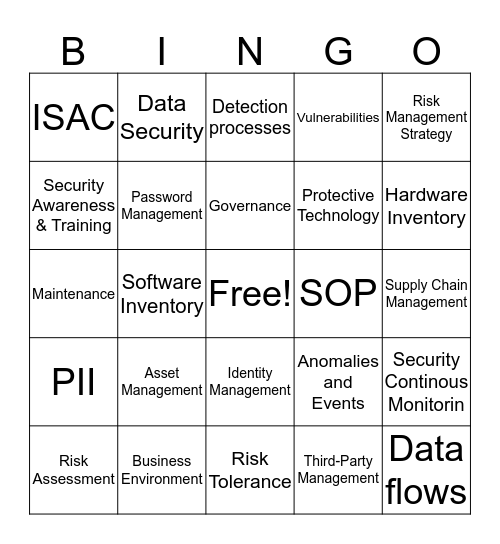
This bingo card has a free space and 24 words: Asset Management, Business Environment, Governance, Risk Assessment, Risk Management Strategy, ISAC, Security Awareness & Training, Data Security, SOP, Identity Management, Protective Technology, Maintenance, Anomalies and Events, Security Continous Monitorin, Password Management, Third-Party Management, Supply Chain Management, Detection processes, Hardware Inventory, Software Inventory, Data flows, PII, Vulnerabilities and Risk Tolerance.
Technology Bingo! | Logistics Data Bingo | Bu!! 8h1t BINGO | Logistics Data Administartion | Logistics Data Bingo
Share this URL with your players:
For more control of your online game, create a clone of this card first.
Learn how to conduct a bingo game.
With players vying for a you'll have to call about __ items before someone wins. There's a __% chance that a lucky player would win after calling __ items.
Tip: If you want your game to last longer (on average), add more unique words/images to it.